Security
Security and reliability of data computing processes absolutely come first.
Since we conduct our operations within the fenced off and guarded NCBJ premises in Świerk, our buildings are physically protected to the highest security standards. Other benefits of that localization include also access to well-developed infrastructure, including reliable power supply. Reliability is guaranteed by two independent service lines linking NCBJ Research Centre in Świerk with the national power grid.
On top of that, our operations are backed-up by a 1,25 MVA Diesel generator we may run in extraordinary emergencies and 4 UPS units each of 300 kVA power.
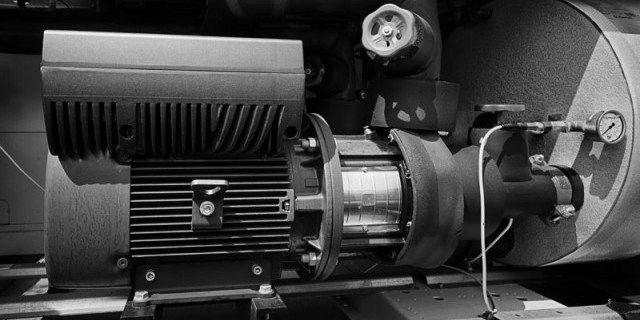
Our computing hardware is cooled down by two independent and highly reliable loops each of 850 KW cooling power with modern variable delivery circulation pumps. External glycol-based loops linking heat exchangers with refrigerating units installed on the building roof are equipped with three pumps each of 11 kW power. Two of them are sufficient to generate the rated chilling power, the third one is installed for redundancy. Similarly, two pumps are installed in each of the two internal water-based loops linking heat exchangers with server cabinets: one of them is running the loop, the other backs the loop operation up. Each of the four pumps has 18.5 kW power.
System refrigerating units are composed of high-performance scroll compressors installed on roof of the CIS main building. Power of each set of the compressor is about 430 kW. The devices may operate all year round at ambient temperatures within the 20…+35°C range. For ambient temperatures below 12°C the system is cooled exclusively with air. Glycol-based loop compressors are engaged automatically only for temperatures above that threshold (and depending on the current system load). Two refrigerating units have been installed in the first stage of the development. However, space for up to five units (four operational units and the fifth redundant one) has been reserved.
The main building of the Świerk Computing Centre project has a special room that meets the technical requirements for the Classified Document Register, it is also possible to extract part of the resources to handle the classified data.
Proper IT/administrative solutions help to attain a high level of data computing security. Access to CIŚ computational infrastructure is accomplished via a PKI-based VPN (Virtual Private Network based on Public Key Infrastructure). A KERBEROS-based central authorisation system manages all operations of logging into our network.